The Data Protection Officer (DPO) is not only responsible for ensuring compliance with legislation and timely reporting but must also report to management in case of a data breach. This article discusses the standard operating procedures (SOPs) for what happens in the event of a data breach and how the DPO may report to their management.
Quick Reference Guide on Reporting
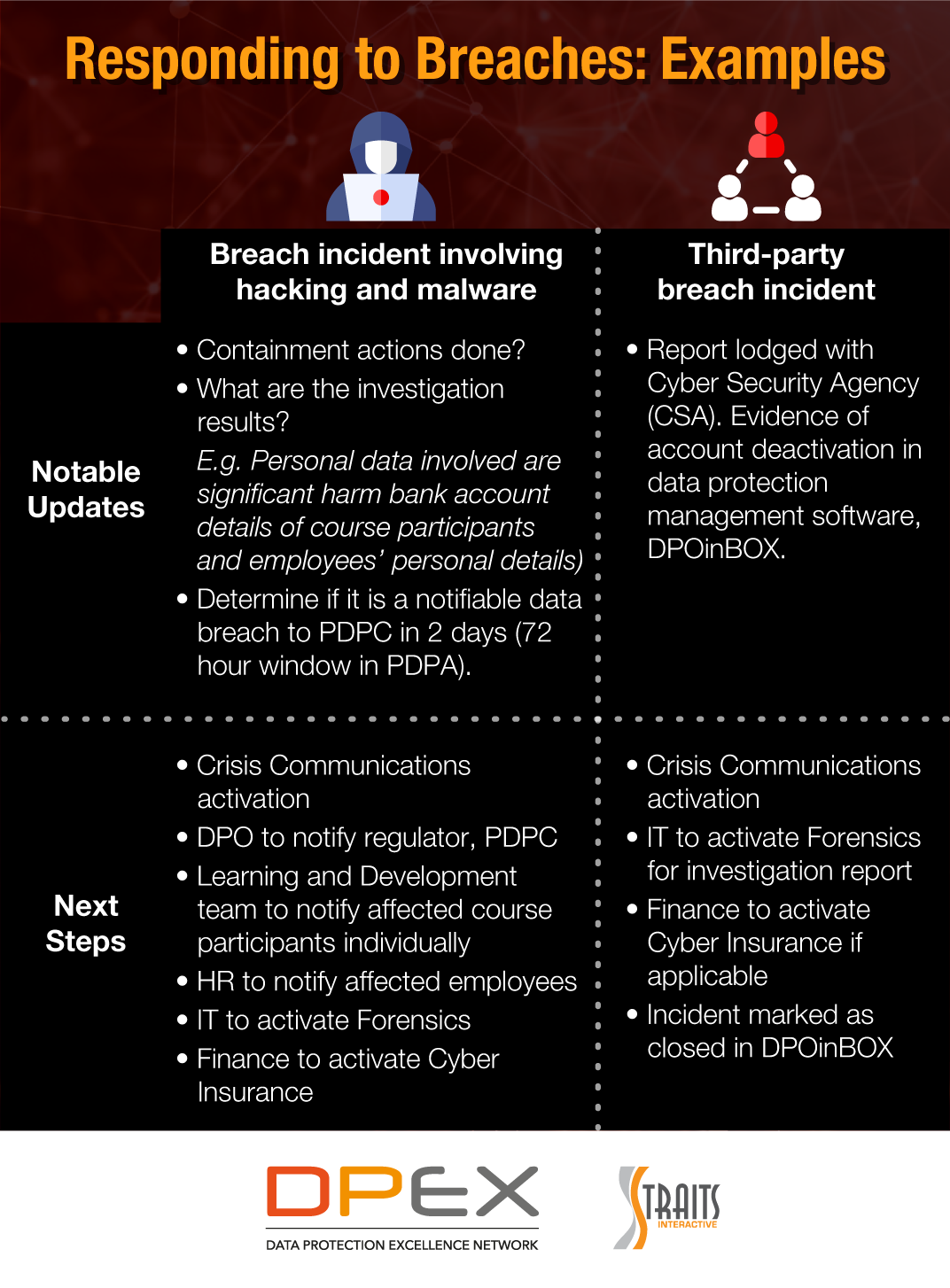
Before a DPO reports to management, they must first ascertain if the breach incident arose due to internal staff error, hacking, malware or a third-party breach. It is important to identify the breach so that the organisation can react appropriately with their breach management plan.
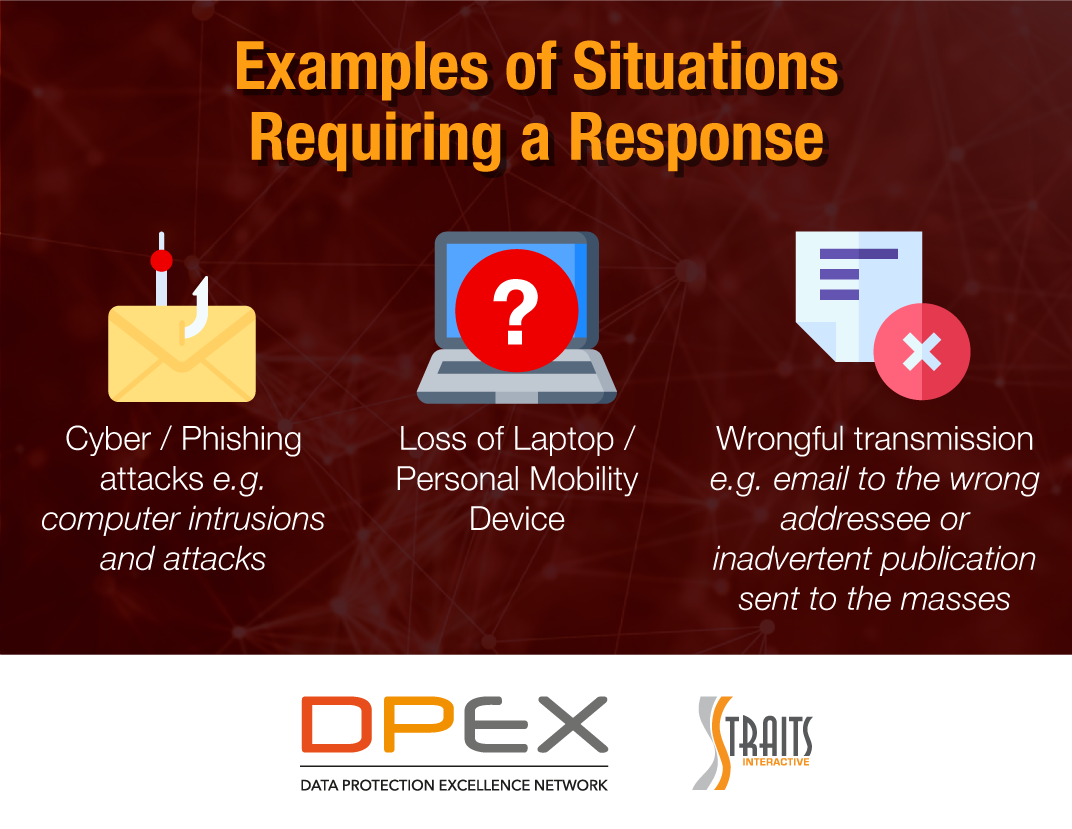
Some examples of situations requiring a response include:
- Cyber / Phishing attacks, e.g., computer intrusions and attacks
- Loss of Laptop / Personal Mobility Device
- Wrongful transmission, e.g., email to the wrong addressee or inadvertent publication sent to the masses
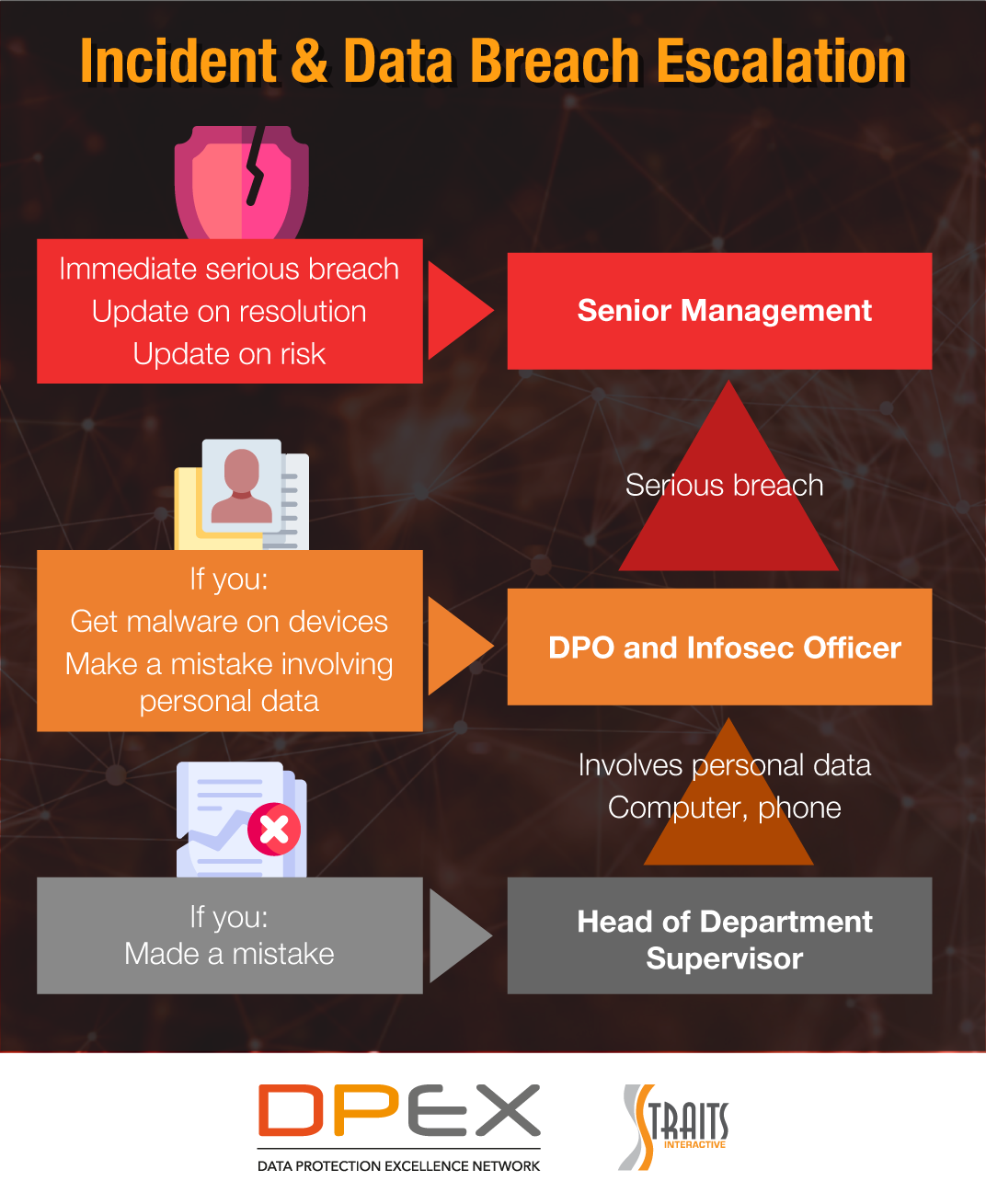
Before determining the nature of the breach, the organisation’s employees must be aware of the steps or standard operating procedures (SOPs) that they have to take if they discover a breach.
SOPs for Responding in case of a Data Breach
- Contact Head of Department as well as DPO to contain the breach. DPO must be involved if the matter involves data breach or data loss.
- Escalation to the Data Breach Management Team (CEO, Head of Risk, Head of IT, Head of Marketing).
- Response Committee comprising all relevant departments and external legal counsel (if required).
- Follow ”Drawer Plan” for breach scenario
The DPO and organisation should also know which agency to contact when they have identified the nature of a data breach incident.
Agency to Report to
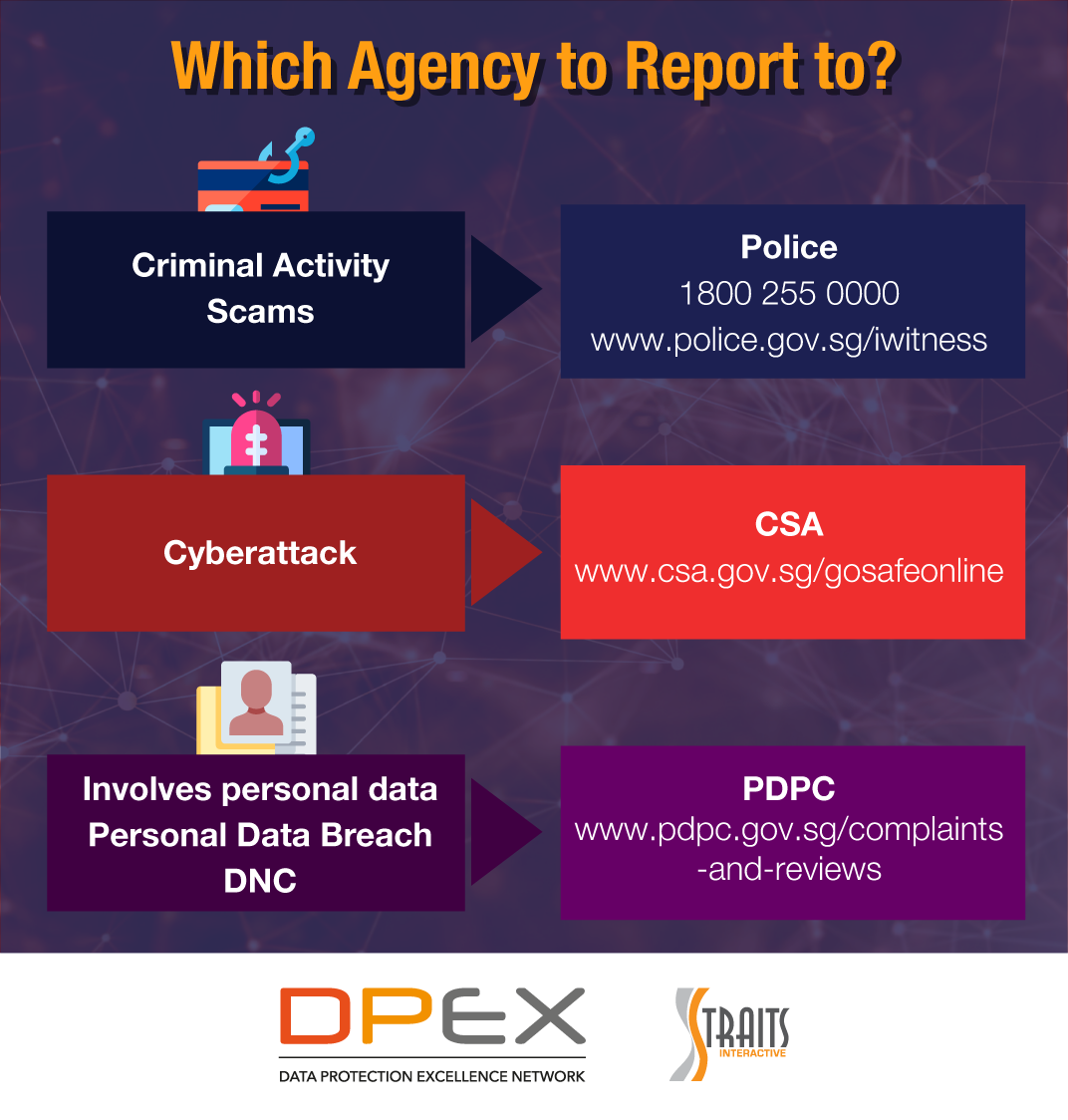
As shown in the diagram, reporting should be done to the following agencies:
- Criminal Activity or Scams
Police | 1800 255 0000 | www.police.gov.sg/iwitness - Cyber Attack
CSA | www.csa.gov.sg/gosafeonline - Involves Personal Data | Personal Data Breach | DNC
PDPC | www.pdpc.gov.sg/complaints-and-reviews
Conclusion
Due to the evolving nature of technology and its increasing use in daily life and business life, new cybercrimes are being developed or committed on a frequent basis. These crimes range from totally new technologies to committing types of cybercrimes to apply previous cybercrime methodologies to new targets as new technology is embraced. Cybercrime has become so prevalent, that many people are more worried about cybercrimes such as identity theft than home burglaries.
Article By: Aman Khajanchi
The views and opinions expressed in this article are those of the author and do not necessarily reflect the official view or position of DPEX Network.