How can software support WFH data protection risks in organisations?
2021-09-07

Data protection and privacy risks have come under the spotlight recently due to accelerated digitalisation brought about by the pandemic. Many employees have found themselves in work-from-home (WFH) situations during the last 18 months. WFH has brought about benefits for both businesses and employees, the biggest of which is business continuity, but have we considered the data protection and privacy risks that come with WFH?
Benjamin Shepherdson, Straits Interactive’s Malaysia Country Manager, speaks to Ng Quan Cheng, IT & Info Security Manager at Straits Interactive, to learn more about IT challenges that have arisen from WFH, and the measures needed to minimise data security risks.
Ben (B): From an information security perspective, how do you ensure data security when working from home? What are the types and levels of protection and the controls that can be put in place?
Quan Cheng (QC):
The two main things that IT has to take note of are:
- Employee’s device e.g., laptop
- Employee’s home network i.e., Wi-Fi
Device
There must be encryption put in place to protect the data stored within. This is especially important when anticipating scenarios such as loss or theft of the device. Encryption prevents unauthorised access to data stored, for example, in a laptop or a tablet.
Recommendation: Bitlocker for Microsoft Windows devices and FileVault for Apple macOS devices provide adequate protection.
Other than that, patch management is also critical. As many people are in WFH situations now, this is an opportunity for hackers to prey upon and exploit any vulnerabilities. As such, we have been seeing Microsoft and Apple offering patches almost every month to address this.
Recommendation: Companies can deploy remote monitoring management tools to protect the device.
Home Network
When using devices outside of the office network, it is essential for employees to have antivirus software installed on their laptops. Antivirus software will help protect the laptop from viruses, including malware and ransomware.
Recommendation: In addition to antivirus software for devices such as laptops, companies should advise employees to ensure that their home router is installed with its latest software, also known as firmware. This firmware will ensure that the router is patched, or has the most updated fixes and improvements. Next, the Wi-Fi security settings should use encrypted passwords based on sophisticated standards, e.g. WPA2/AES, instead of a simple password (list of 8-10 characters with symbols, etc).
B: There are two types of antivirus, corporate and consumer/individual - what is the difference between the two versions?
QC: The difference between personal and corporate antivirus software (paid versions):

For personal antivirus, it is more suited for individuals. For a corporate antivirus, the IT administrator can preconfigure it to protect not only the device itself but also the company email system that it is using.
For instance, staff could be using their personal devices instead of company-issued devices, and they may prefer using Microsoft Outlook as their personal email client, but their employer may implement Gmail as the corporate email system. In this case - if employees purchase personal antivirus software, it would only protect their personal email in Microsoft Outlook; they would not be able to use their personal antivirus to protect the company’s email system.
B: When working from home, who is responsible for data security and data protection - the company or the employee?
QC: When working from home, both the company and the employee are responsible for data security and data protection.

B: How do you ensure that employees remain updated on data protection policy especially on new policies that arise from WFH arrangements?
QC: You can disseminate information through communication channels like WhatsApp, Telegram or email.
In Straits Interactive, we disseminate information through our company chat group and our DPOinBOX software. The DPOinBOX software enables us to capture the acknowledgement of the employees, that they have read and understood updates.
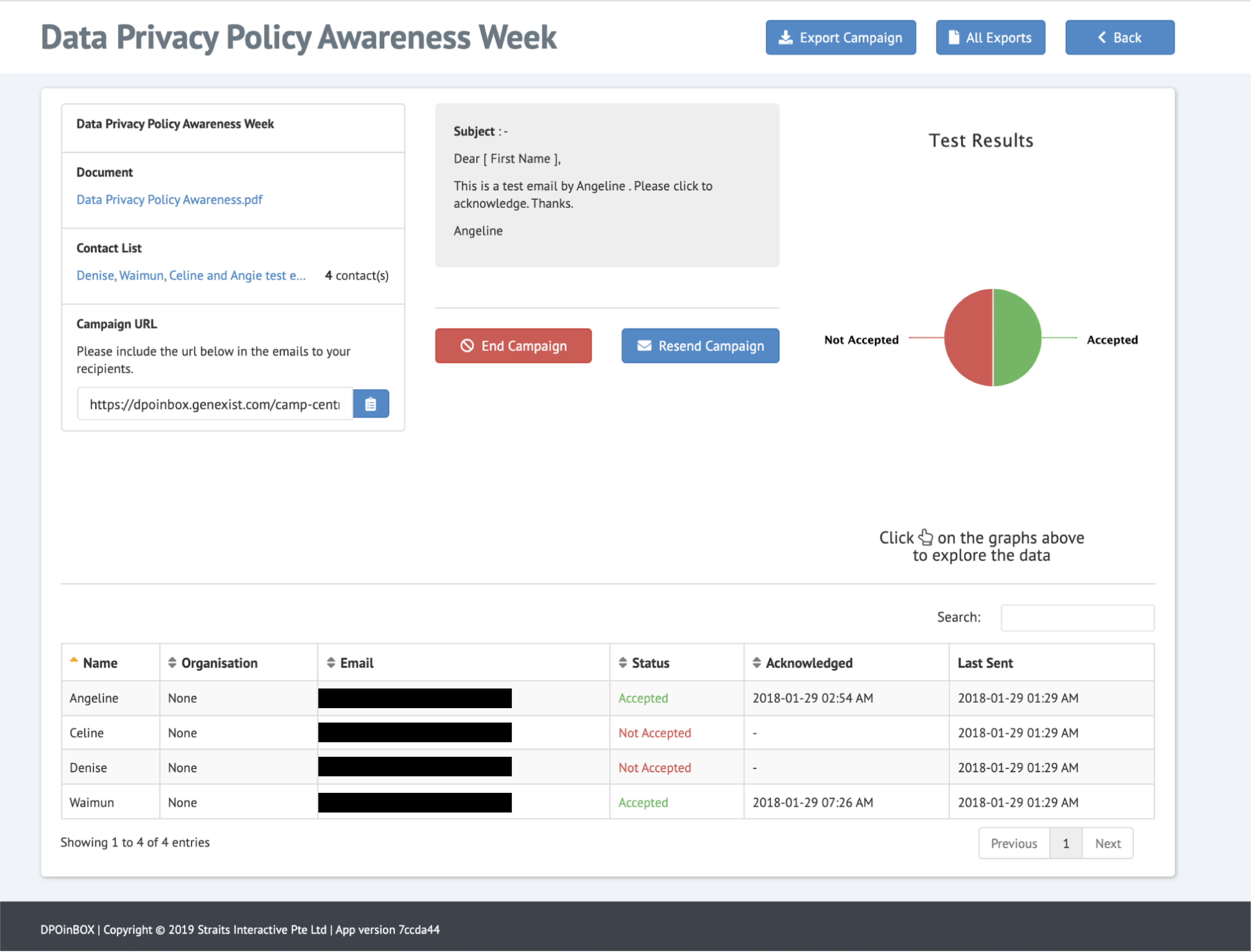
Diagram: Records of employees receiving and acknowledging an update
- What types of information do we disseminate?
In Singapore, we are fortunate to have the Cyber Security Agency of Singapore (CSA) publishing notifications of potential vulnerabilities. We can leverage on these updates by adapting their contents and disseminating the information in layman terms to our staff across various departments. It is also helpful to incorporate real-life examples for better understanding.
B: How can IT personnel assist employees remotely during WFH? Do you have any examples to share with us?
QC: IT can use remote access tools such as “quick assist” for Windows or utilise paid remote monitoring tools like TeamViewer. With remote monitoring and access tools, IT can aid company employees by helping to troubleshoot and resolve their problems efficiently.
However, it is important for IT to conduct due diligence on these remote monitoring or access tools, to determine if they are suitable for the organisation’s use. For instance, IT can check if the company providing the software service has ISO 27001 and ISO 27701 certification.
B: What are some of the common data protection risks when working from home?
QC: Outdated patches or lack of suitable antivirus software.
As employees are not in the office, there could be instances where the central system fails to push and install a software update on their laptops. It may be insufficient to rely purely on automatic system updates. By deploying a remote monitoring and management tool, IT and perhaps the company’s DPO can churn out reports, such as for the patch status of all laptop devices in the company. From the reports, the IT team can easily identify vulnerable devices and help ensure they are updated with the latest protective software. The remote monitoring and management tool also facilitates in reporting to management about the status of the network and in evaluating if the existing policies and processes are sufficient.
B: Were there any challenges you faced in implementing WFH policies and processes? If there were challenges, how did you resolve them?
QC: This may be the case for most organisations, but some people will find it difficult to adapt to change. For certain employees, they may have the mindset that [WFH policies and practices are] additional tasks for them or an extra area to take note of. They may view it as hindering their productivity. Another issue would be that employees may also be worried about being remotely monitored. However, this can be resolved with education, to provide assurance that adopting data security best practices benefits everyone, including staff and other stakeholders.
B: Can you share with us the typical procedures to execute remote monitoring and access tools?
QC:
1. Communicate with the employee e.g. text message/call
- Inform them that the remote monitoring and access tool will initiate a prompt and they should accept the request.
- After 30 seconds, if the employee does not accept the request, it will expire.
2. After the request has been accepted, IT can proceed to manage remote access and help to troubleshoot and resolve any future issues
B: Is it necessary for organisations to implement paid remote monitoring management software?
QC: For small companies with resource constraints - if all of their employees’ devices are on Windows, the pre-installed “quick assist” function may be sufficient. Otherwise, purchasing remote monitoring management tools such as Atera may be an option.
Just one more step! We've sent an email to .
Please check your inbox or spam and open it to activate your account.
DPEX Network is a Community Initiative of Straits Interactive.
Copyright © Straits Interactive Pte Ltd. All Rights Reserved.
All intellectual property rights to logos and brands featured on this website remain the property of their respective owners.
