The creation of data has been exponential over the last few years which contributes to its ubiquity and is becoming front and center of digital business strategies. On May 8, 2020, IDC published their Global DataSphere forecast which shows continued steady growth in the creation and consumption of data and stated that “the amount of data created over the next 3 years will be more than the data created over the last 30 years”. In the same report, it also claims “Video surveillance data and privacy and regulatory initiatives/mandates continue to intersect with one another. Finding the correct balance between security, personalization, efficiency, and individual rights to privacy will be one of the great tensions of this decade.” More than ever, there is a mounting need for organizations to integrate privacy and data protection to achieve an equilibrium between the achievement of business objectives and individual data privacy. Globally, there are now more than 200 countries with some form or another of a data privacy regulation based on the report of the United Nations Conference on Trade and Development (UNCTAD).
The publication of ISO/IEC 27701 (Privacy Information Management System) in 2019 as an extension of the existing ISO/IEC 27001 (Information Security Management System) provides a process approach for organisations to naturally augment their existing information security practices to the protection of personally identifiable information. ISO/IEC 27701 leverages on the company’s existing information security policies and procedures. The two standards are designed to help organisations of any size or complexity from any industry to establish, implement, operate, monitor and maintain both information security and privacy management systems.
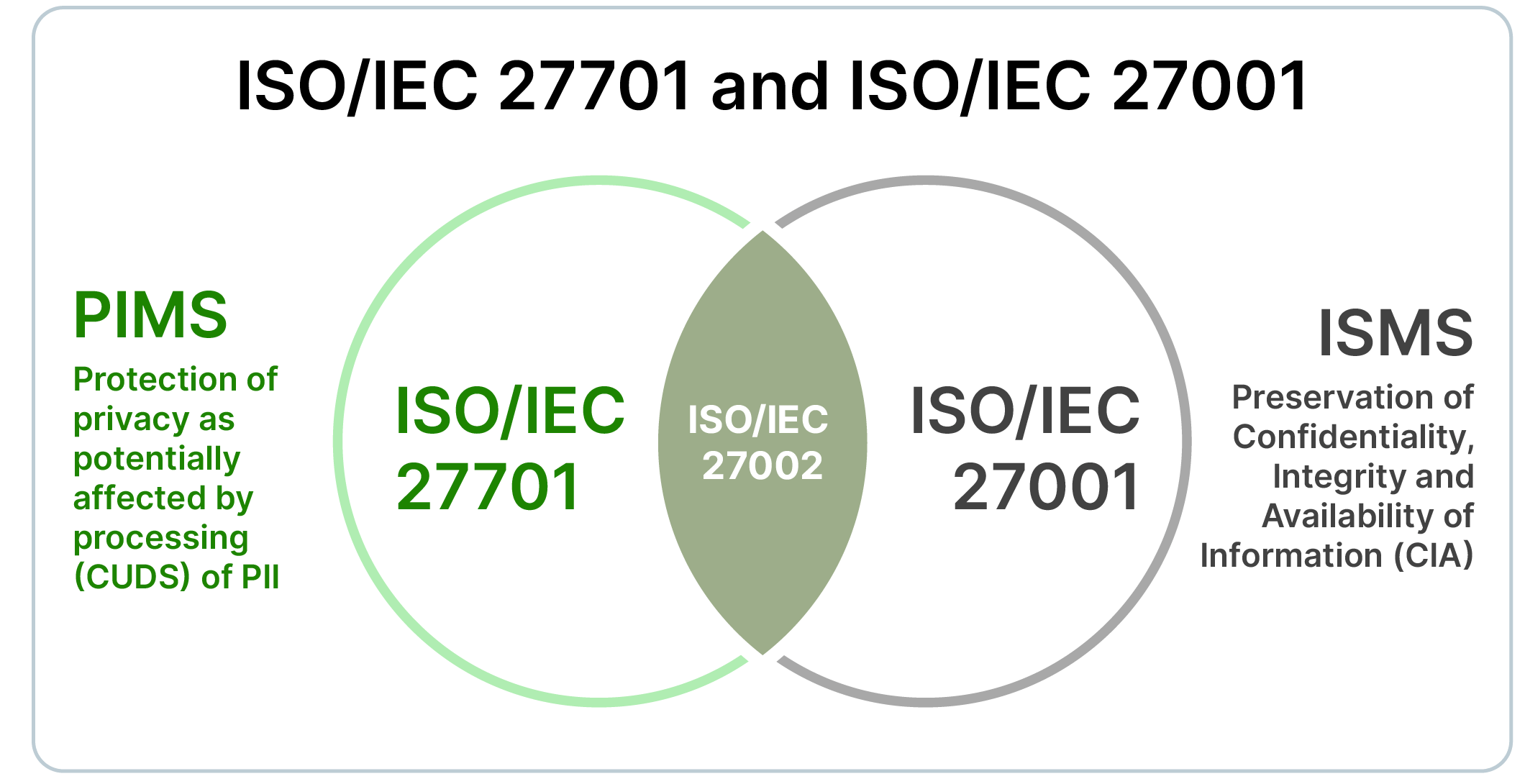
Looking at the Venn diagram, privacy information management system and information security management system share the control elements of ISO/IEC 27002 which Data Protection and Information Security Officers can utilise in their implementation of management systems.
Privacy (CUDS) - ISO/IEC 27701 (PIMS)
Governance of Authorised Access - Protection of privacy as potentially affected by processing (CUDS) of PII
Security (CIA) - ISO/IEC 27001 (ISMS)
Governance of Unauthorised Access - Preservation of Confidentiality, Integrity and Availability of Information
The benefits of implementing ISO/IEC 27701
Conformity with the ISO/IEC 27701 provides concrete advantages to the organisation.
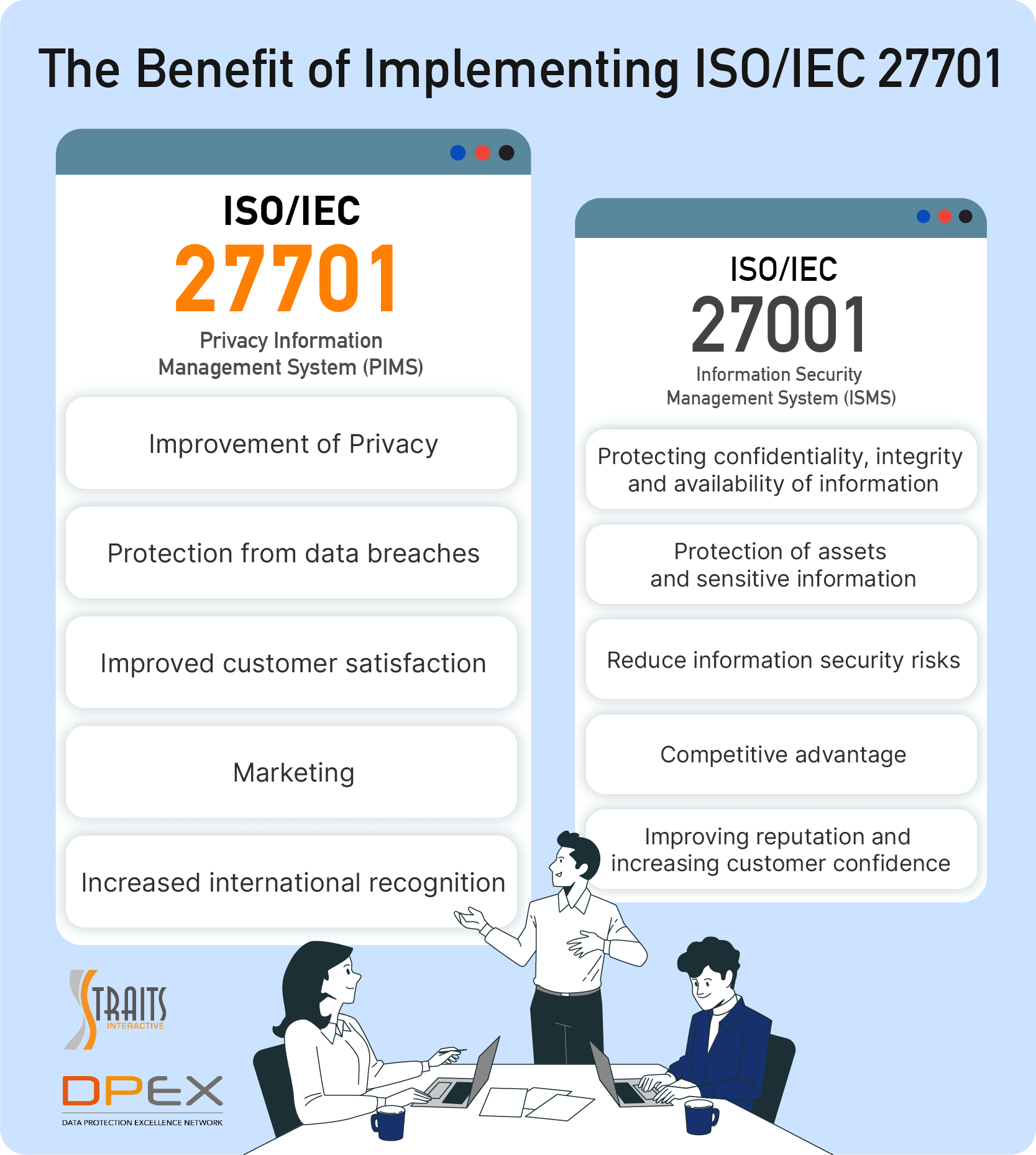
The ISO/IEC 27701 also provides additional guidelines for PII controllers and PII processors. Likewise, it fully supports GDPR by laying out the framework to map its various clauses with the regulation’s articles.
Getting Started on the ISO 27701 Journey
Data Protection Excellence Network (DPEX) offers live online training classes on the ISO/IEC 27701 that will help support advanced professional competency with internationally acknowledged ISO standards. For more information, visit the course page here!
You can have security without privacy, but you cannot have privacy without security. Privacy includes the laws/regulations requiring organisations to protect personal data and security is the method to protect that data.
Article By:
Leong Wai Chong, CIPM, GRCP
Edwin Concepcion, FIP, CIPM, CIPT, CIPP/E
The views and opinions expressed in this article are those of the author and do not necessarily reflect the official view or position of DPEX Network.