Critical digital assets such as personal/company data and financial data that enable e-commerce are becoming increasingly vulnerable due to exponential growth in:
- online transactions,
- variations in regulatory requirements,
- business partnerships and
- outsourcing of services.
These lead to an increased risk in the compromise of the security of data and/or data breach across all industries globally.
Internal Risk from Employees
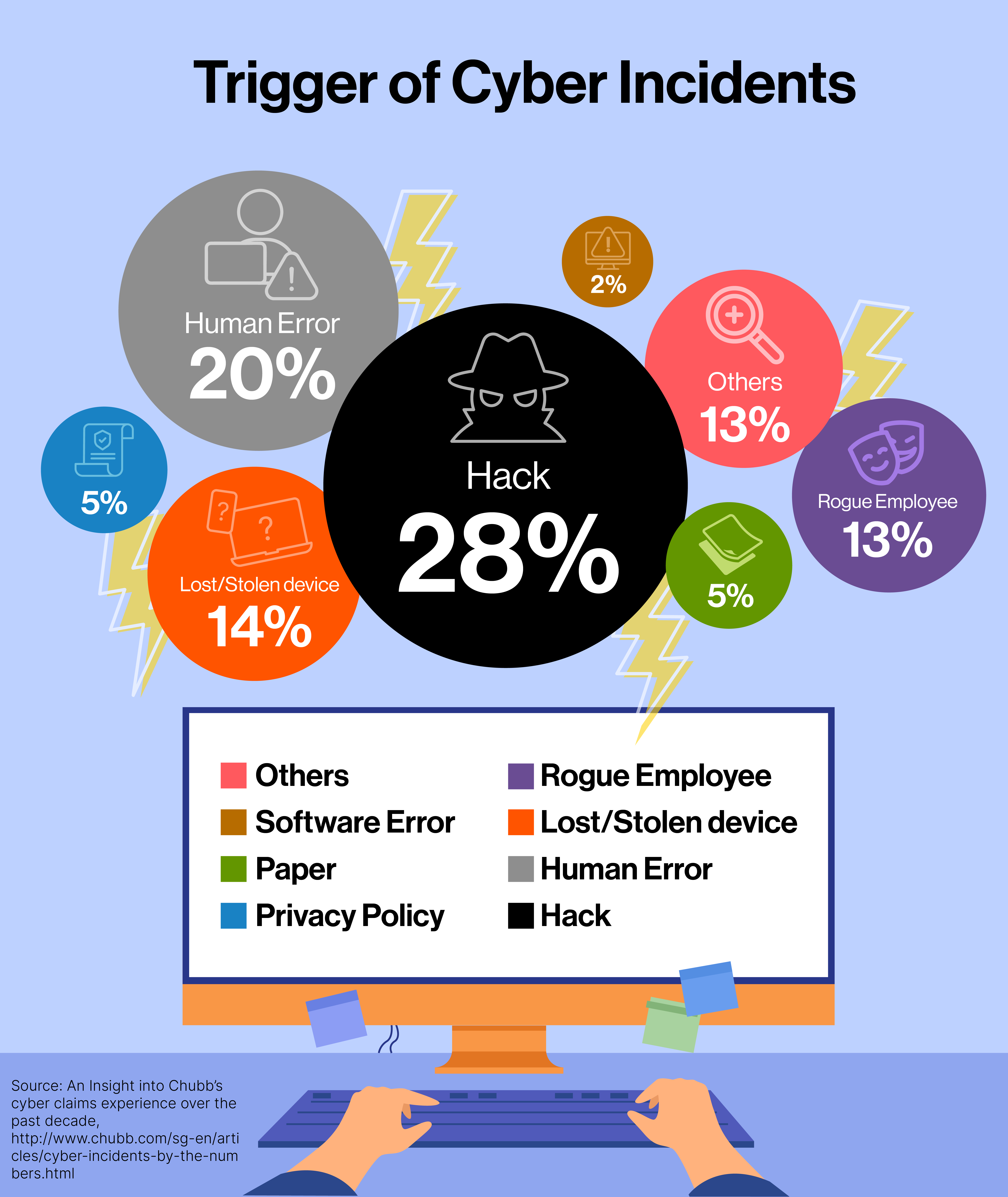
According to an analysis of cybersecurity claims made to the insurance company Chubb in the past ten years, employee-related incidents (insider) account for a significant percentage of the claims. What are internal risks? This is an employee or third-party vendor that has access to a company’s network.
1
Insider risks can be categorised into:
- Unintentional human error - where careless or untrained staff make mistakes that cause a breach, e.g. misaddressed emails, stolen devices, confidential data sent to insecure home systems. Such mistakes can be very costly.
- Malicious or Rogue Employees - whose intent is to steal or damage. They steal sensitive/valuable information for commercial gain, while some have a vendetta against the organization.
- Hacking or Cyber-attack (arising from errors or deliberate co-operation by insider) – Again, more often than not, the system of an organisation is compromised by cybercriminals because of negligence by staff. Through human error, hackers are can hijack identities, often through an unsuspecting employee’s account. They can do this because the organisation does not have a robust data protection security policy. Moreover, often staff is untrained or ignorant of the risks and security policies, allowing malware or phishing attacks through their accounts. Some hackers leverage stolen credentials, especially by gleaning data from social networks.
The most treacherous aspect of insider threats is that the access and activities are coming from trusted systems, and likely undetected. Often malicious employees can even erase evidence of their activities and presence, thus further complicating forensic investigations. In fact, as a combined factor they make up a large part of the cases. .
The Case of a SingTel data leak from an Insider2
In the case reported on 18th March 2021, a team leader of a call centre handling technical support for Singtel customers, was guilty and jailed for leaking data of more than 1,000 business accounts of licensed moneylenders to loan sharks. This was then used to carry out loansharking (harassment to collect debt) activities.3
The culprit was able to access- undetected - over a thousand business accounts of licensed moneylenders and pawn shops, even though it was not part of his job scope. The case came to light only when the police received information that a group of data sellers had been selling statements of call details of licensed moneylenders to unlicensed ones.
Not only was there possibly a breach of Information Security Management System controls, but also clearly an unauthorized disclosure of data and for "illegitimate purposes". There is not enough detail to know if the Data Protection Management System has factored in the risk. Whilst it may have been business contact data, the risk of such leakage (and DPMP) would be part of a wider Governance, Risk and Compliance management (GRC) framework.
Governance Risk and Compliance
In addition to security controls, it is usual for employees to have a profile assessment before joining the organisation. For jobs requiring security clearance, a more thorough evaluation of the personnel is required. Such assessments may even be conducted yearly and employees submit annual declarations e.g. financial standing, renewal of Non Disclosure terms etc but they are not foolproof.
These are part of tasks and events under the GRC management to mitigate risks. In fact, it is from the GRC management framework that the organisation identifies such risks, designs ‘intervening’ events and tasks to mitigate them. The organisation can then assess the risks before and after the interventions. As part of the GRC management, organisations need to have drawer plans to address “what if…”. This helps the organisation to strategise a reaction that mitigates any negative impact.
In the area of data protection, organisations would need to have the expertise to manage risks and factor the following in their plans:
- Understanding data protection regulations and ethics, especially in data and process automation
- Setting up a Governance, Risk, Compliance management programme
- Managing team performance and stakeholders
- Policy and third-party management
- Response to data breach and crisis communication plan
- Business continuity management
Employees can be an organisation’s weakest link, but also its greatest defence. A malicious employee may sell confidential information or even allow attackers entry into the organisation’s network. An ignorant employee may unknowingly leave an “open door” for attackers. However, an employee who is aware of the risks and educated about signs to look out for in a breach is an organisation’s first line of defence. Ensure that employees are familiar with the risks and responses.
Training and Upskilling
In enabling organisations and DPOs to obtain and/or upgrade the relevant data protection skills, consultancy services and training courses are available. The DPEX Network not only provide the basic skill required but a roadmap that enables the DPO to advance his/her knowledge beyond data protection and integrate with GRC and knowledge about international data protection/GRC framework.
Explore the Learning roadmap in:
- Data Protection Advanced Diploma
- Advanced Certificate in Governance, Risk Management and Data Compliance
Do a quick assessment to find out what your organisation needs.
Article By: Leong Wai Chong, CIPM, GRCP
The views and opinions expressed in this article are those of the author and do not necessarily reflect the official view or position of DPEXNetwork.